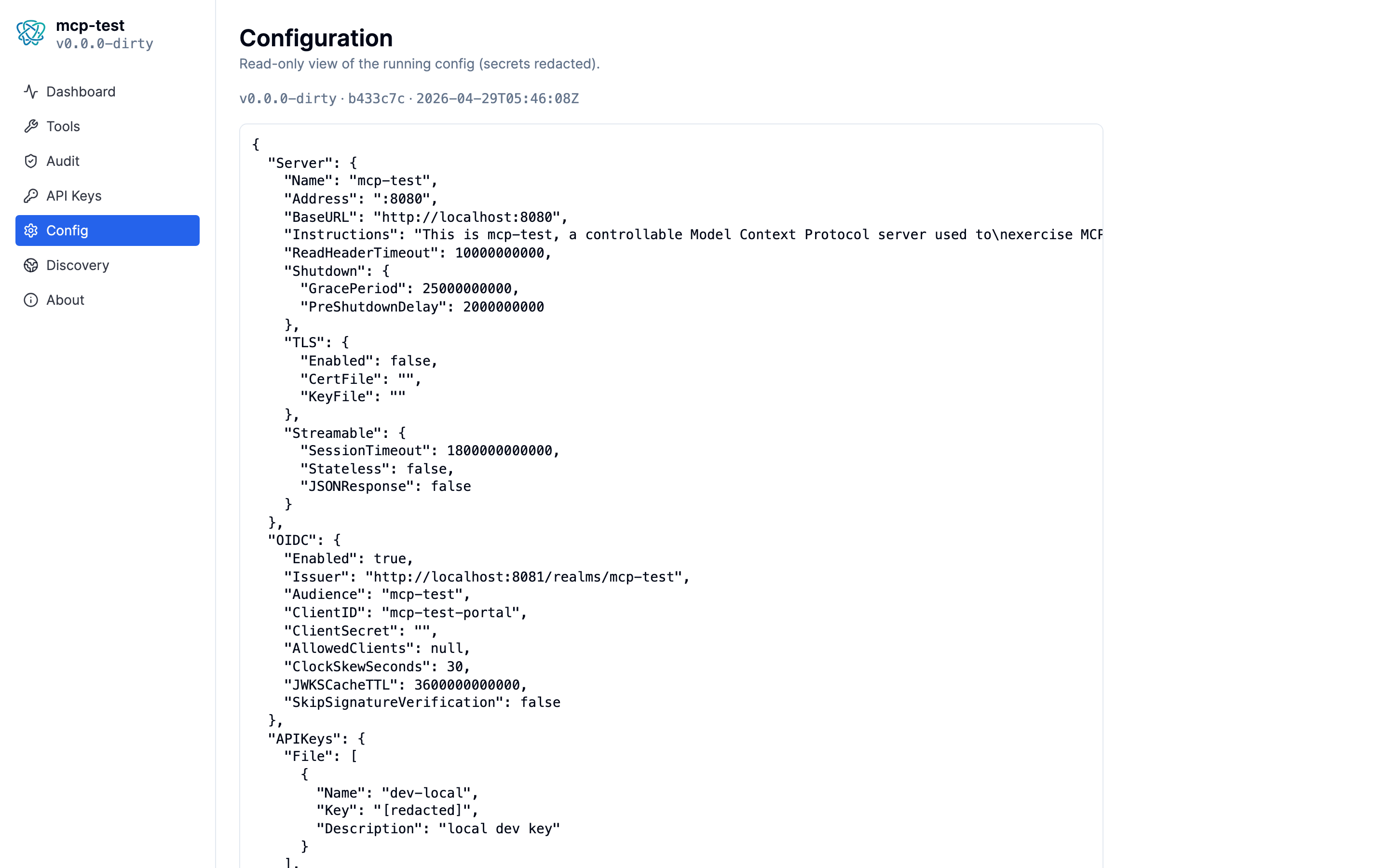
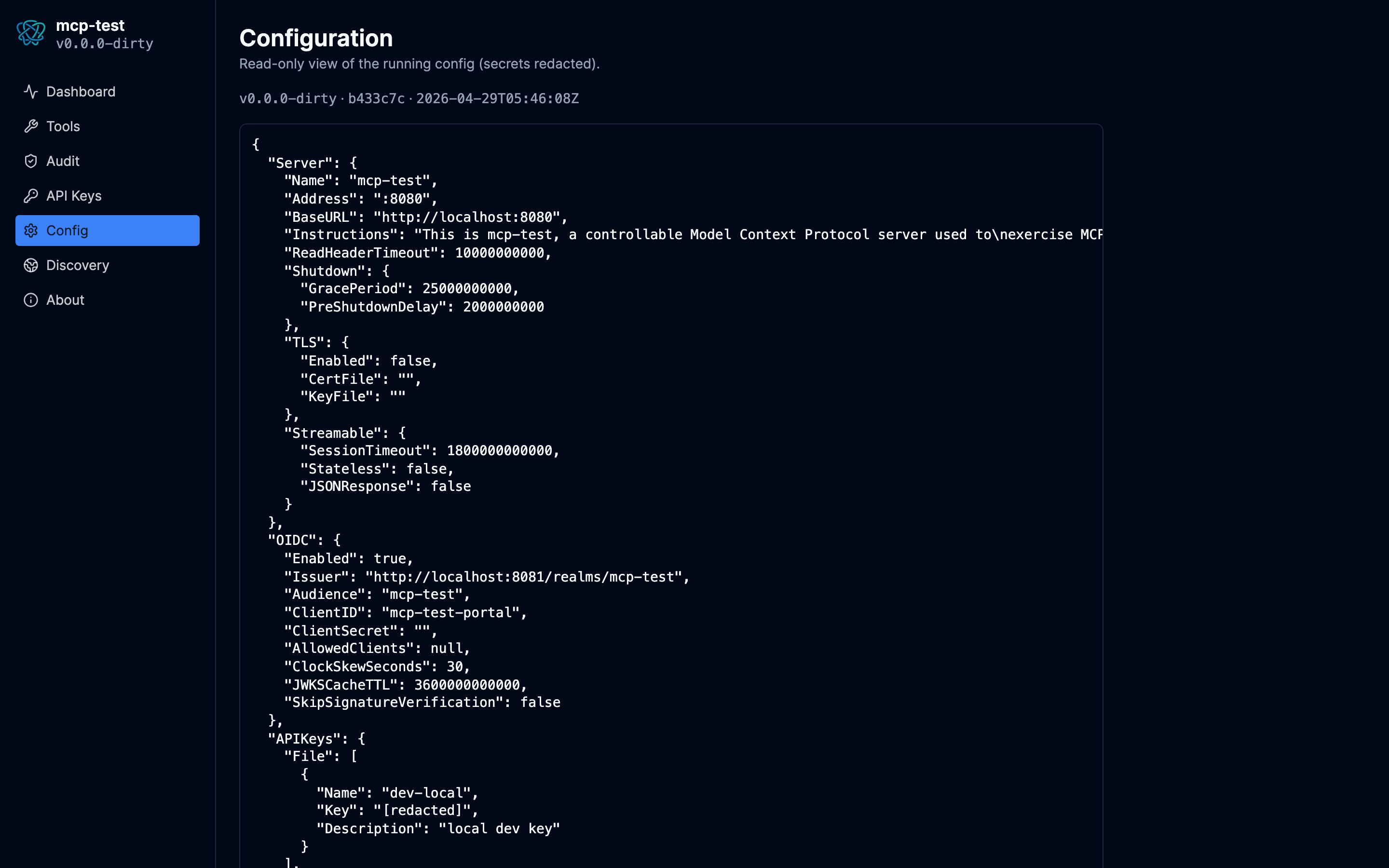
Documentation
mcp-test
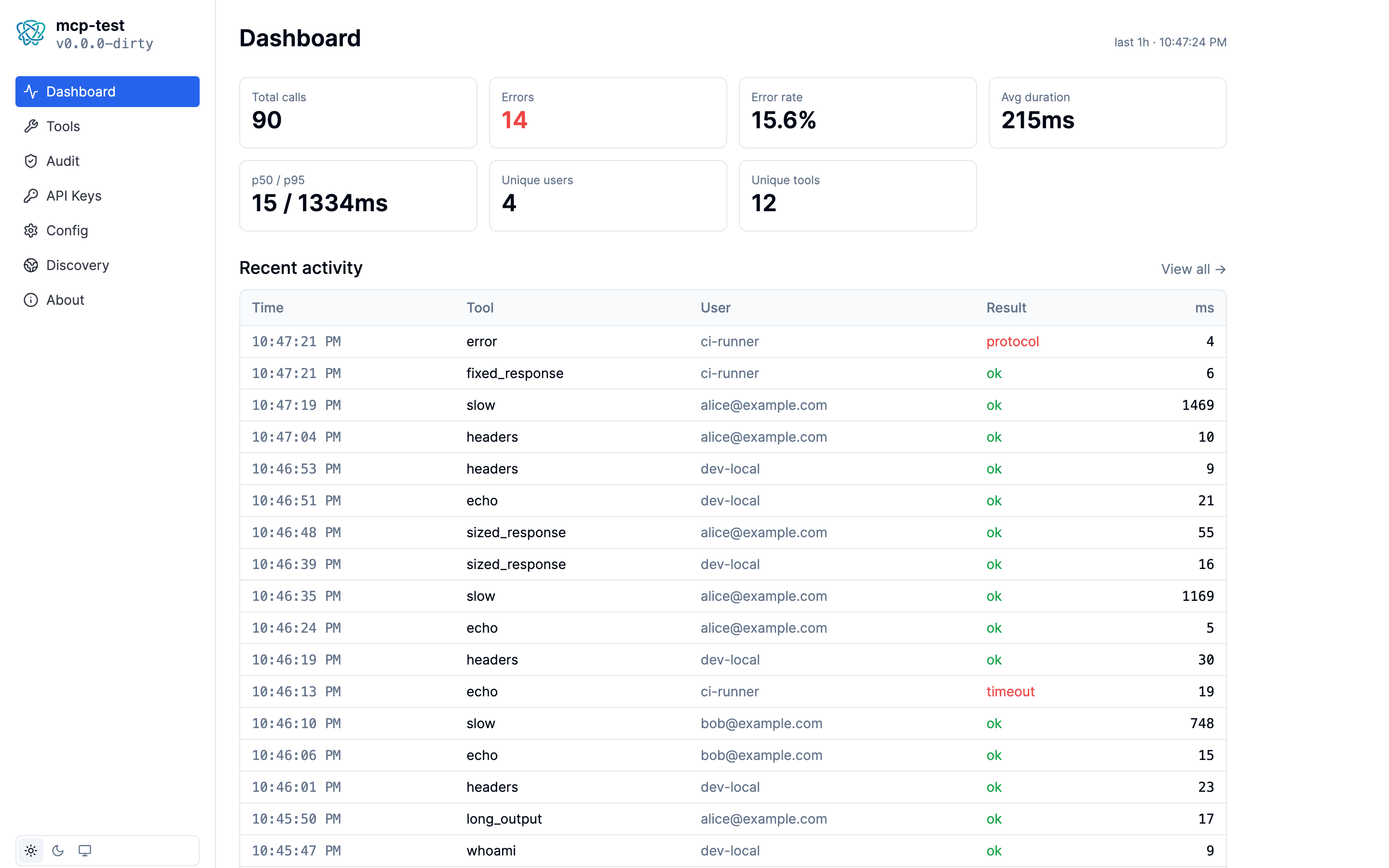
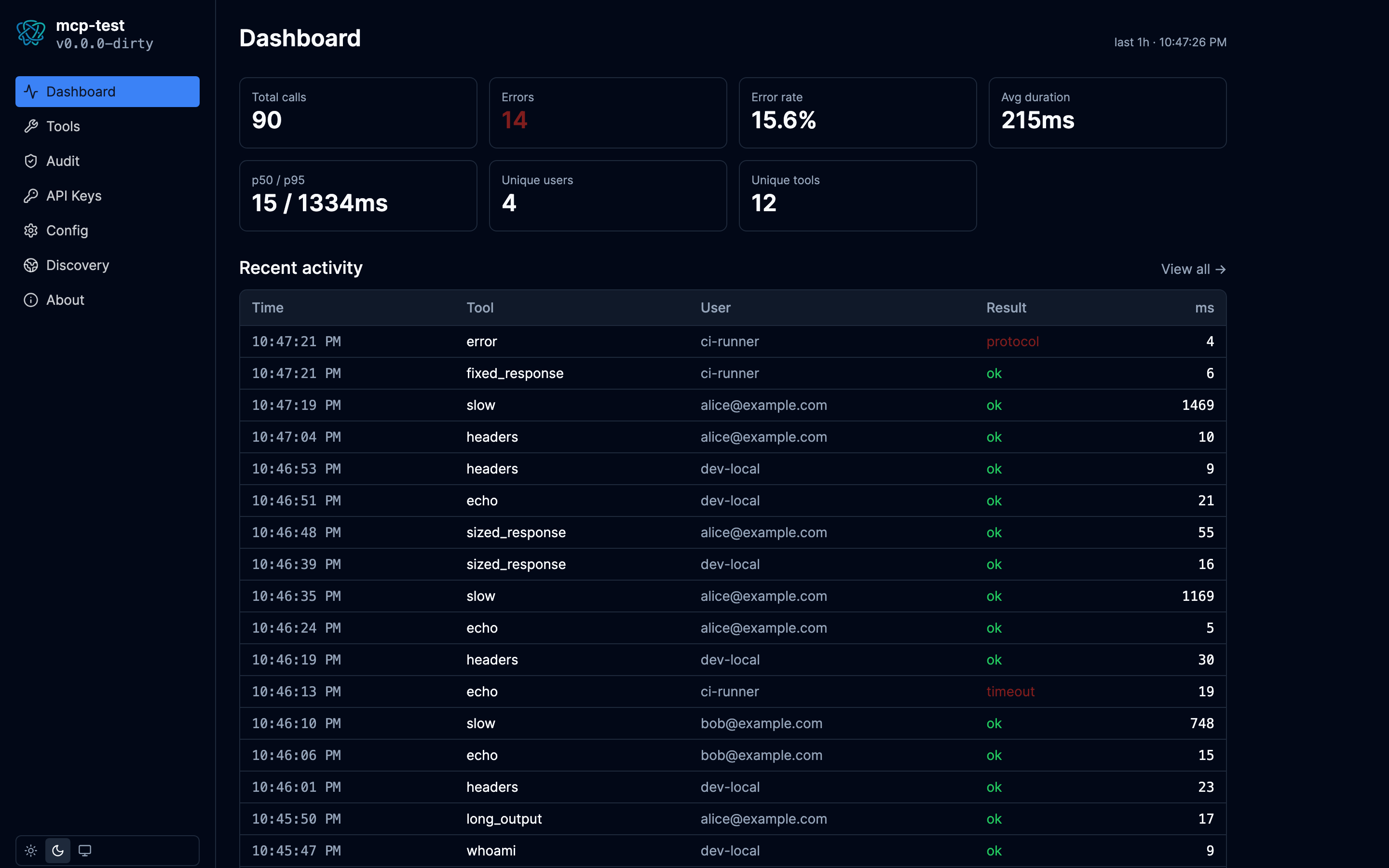
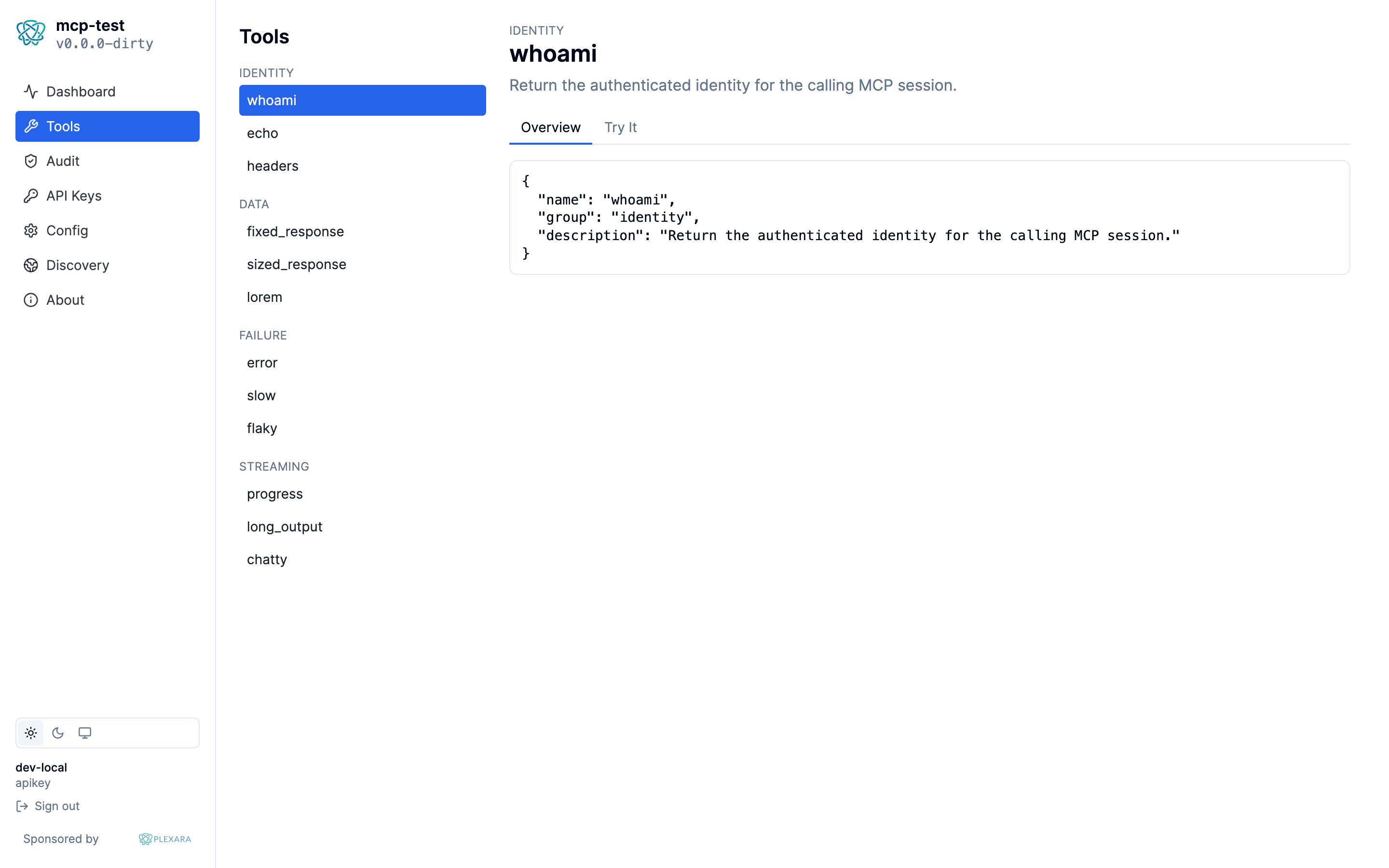
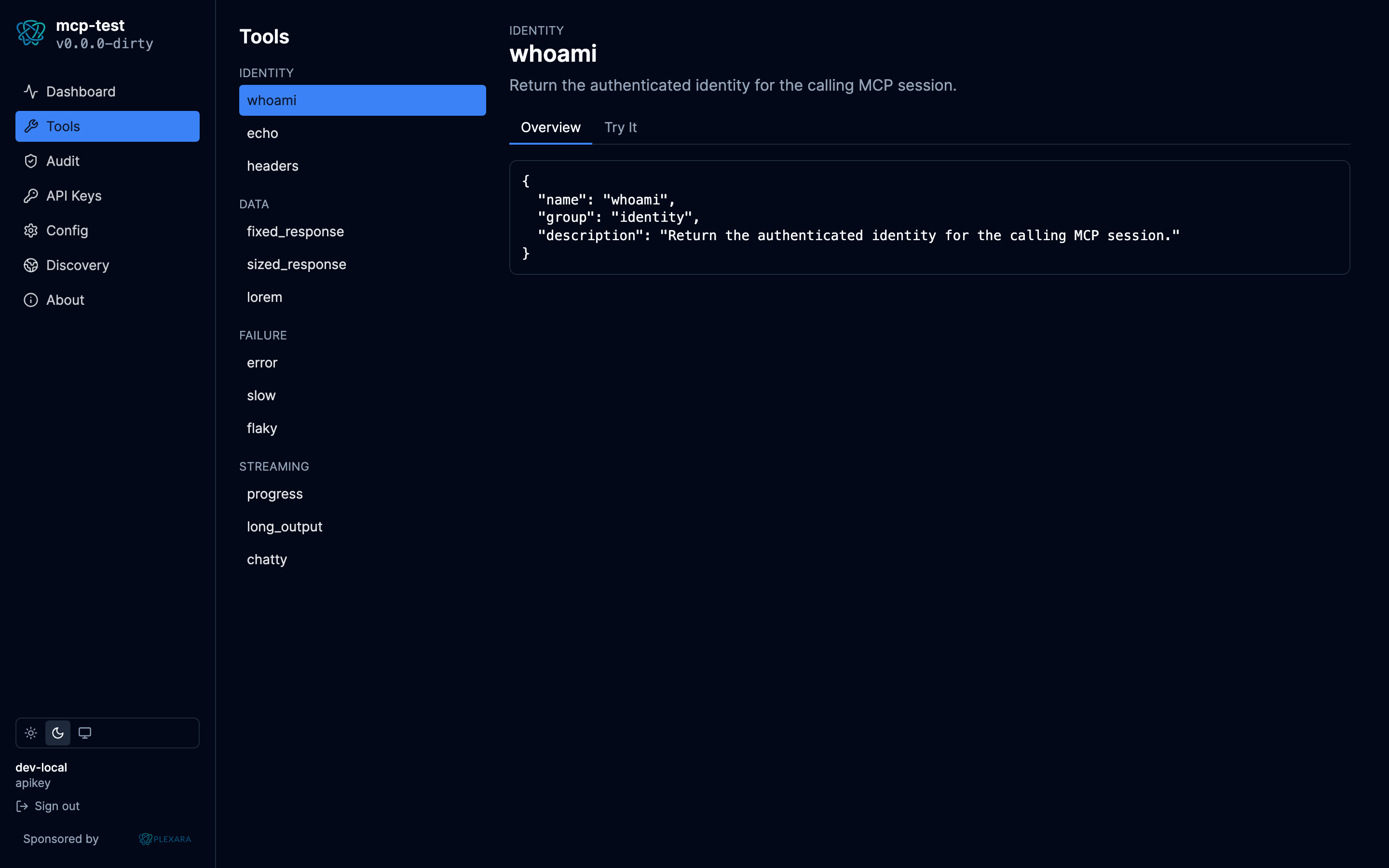
A Model Context Protocol server built as a fixture for testing MCP gateways. Twelve deterministic tools, three auth methods, a Postgres- backed audit log of every call, and an embedded portal for live inspection.
Inspect every call from the browser
Capabilities
The tools are intentionally boring. They return predictable output for predictable input, fail in well-defined ways when asked to, and log every call. That's enough to write end-to-end assertions about a gateway's behavior without depending on real upstream data.
12 tools, 4 categories
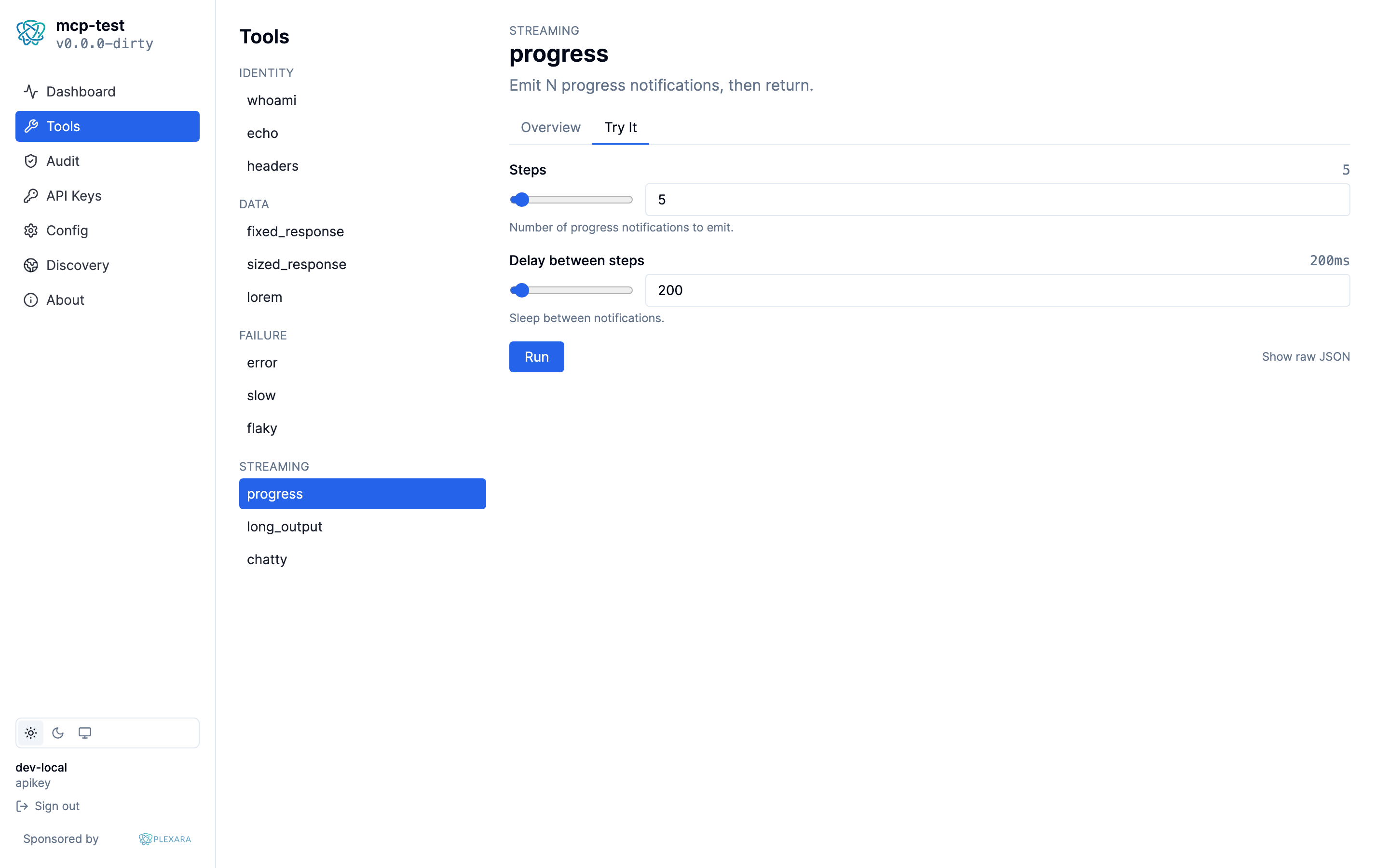
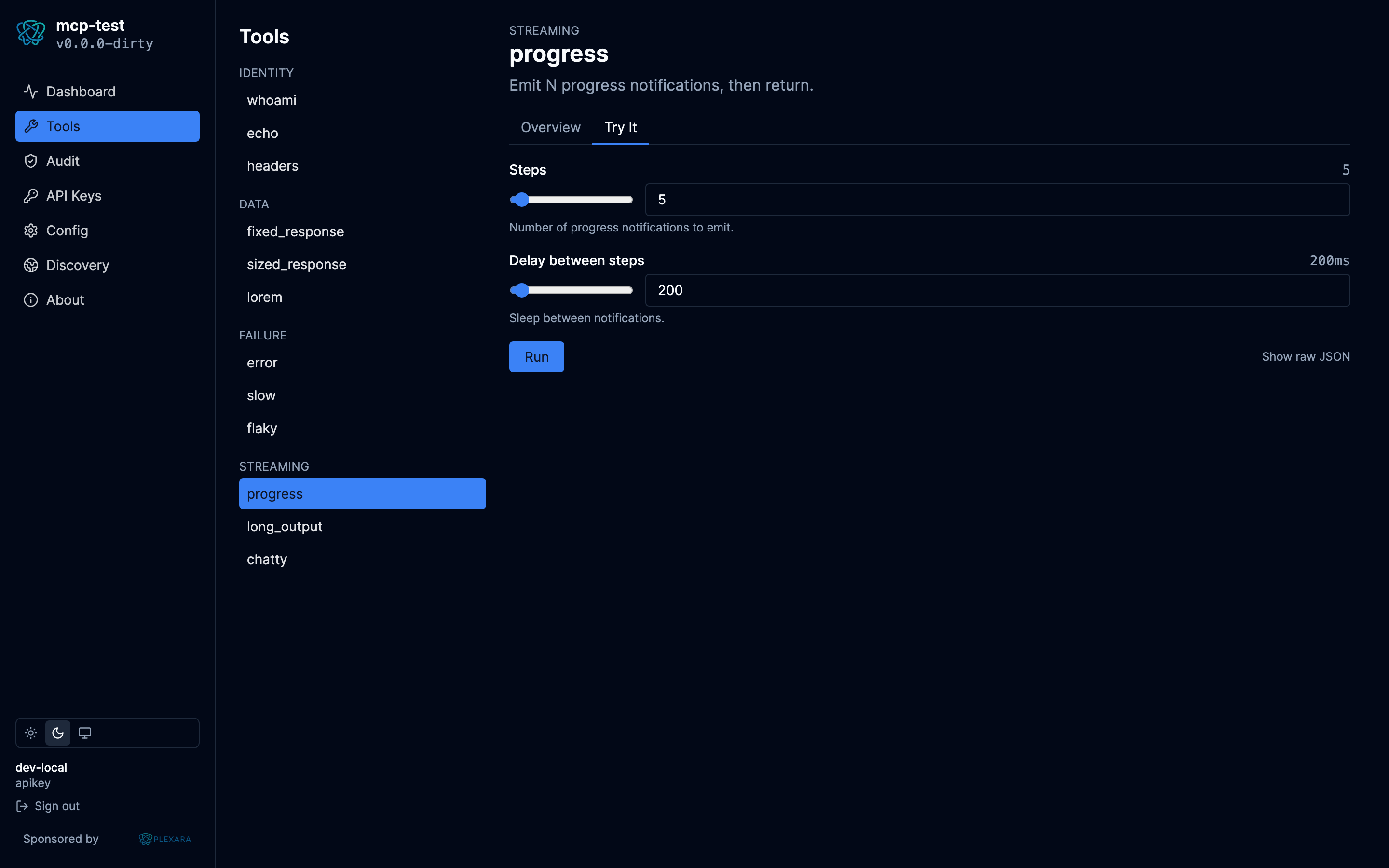
Identity (whoami, echo, headers), data (deterministic fixtures), failure modes (errors, slow, flaky), streaming (progress notifications, multi-block content).
Real auth, three ways
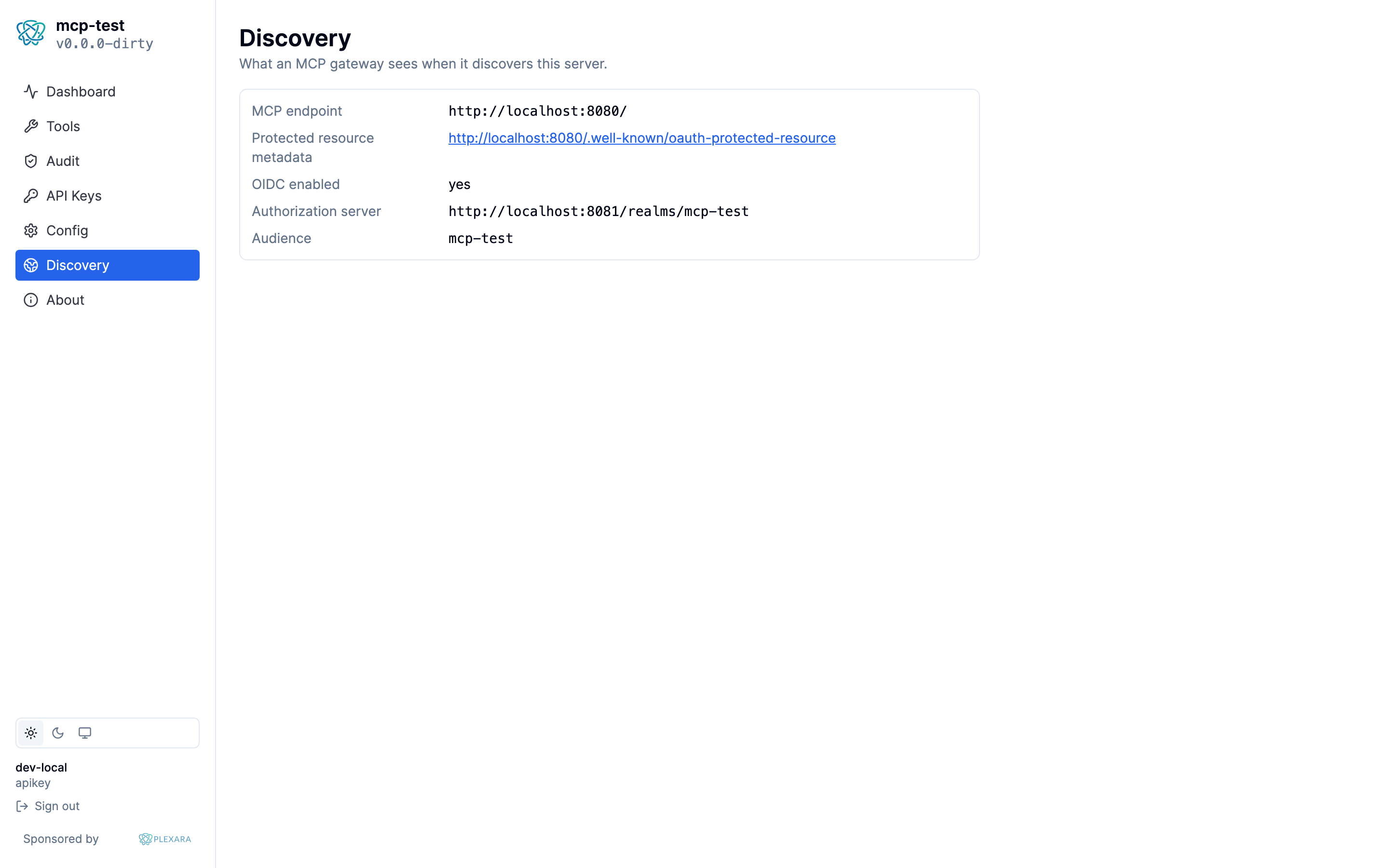
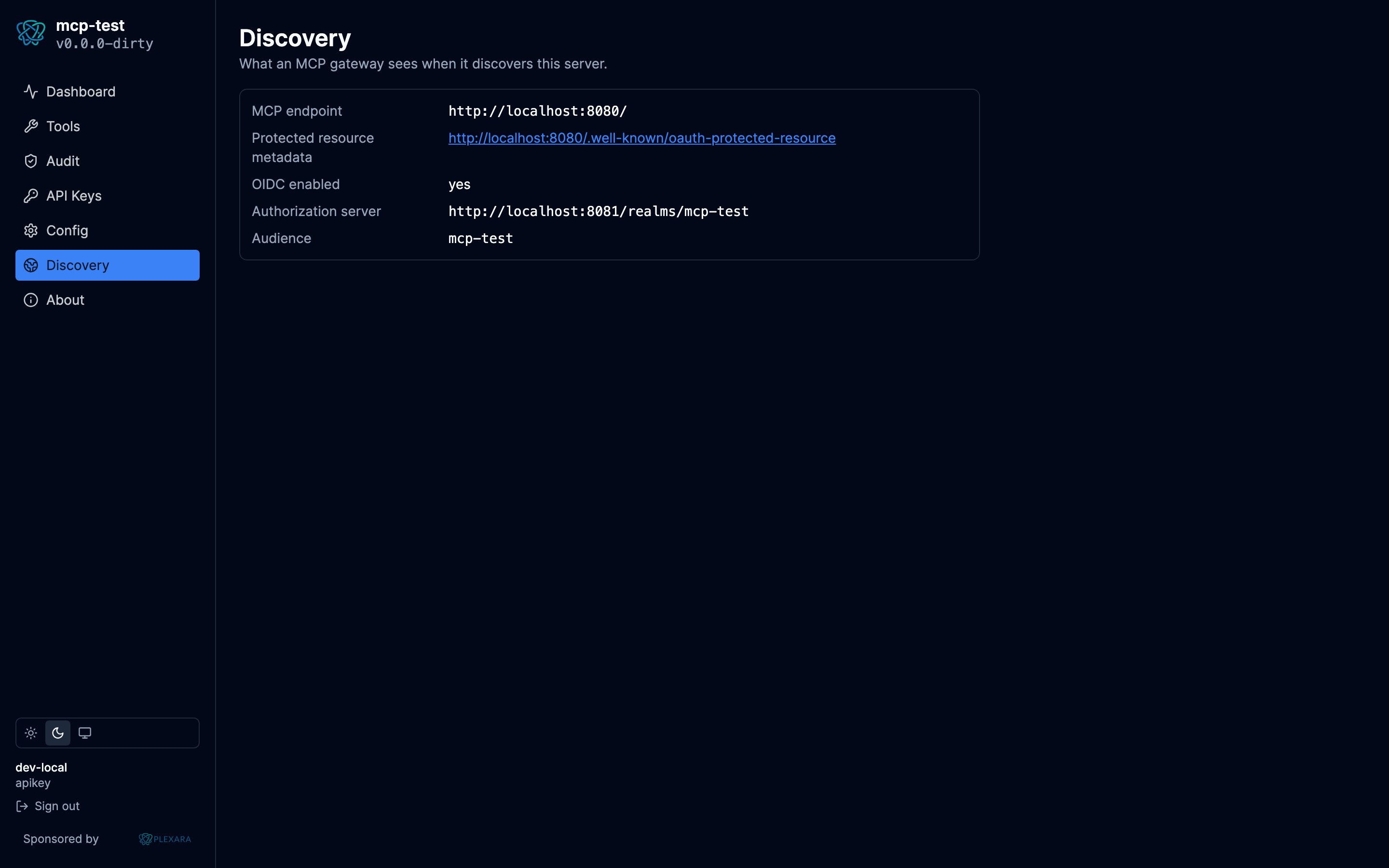
File-loaded API keys (constant-time compare), bcrypt-hashed Postgres-backed keys, and external OIDC delegation with JWKS caching. RFC 9728 protected-resource metadata so MCP clients can discover the issuer.
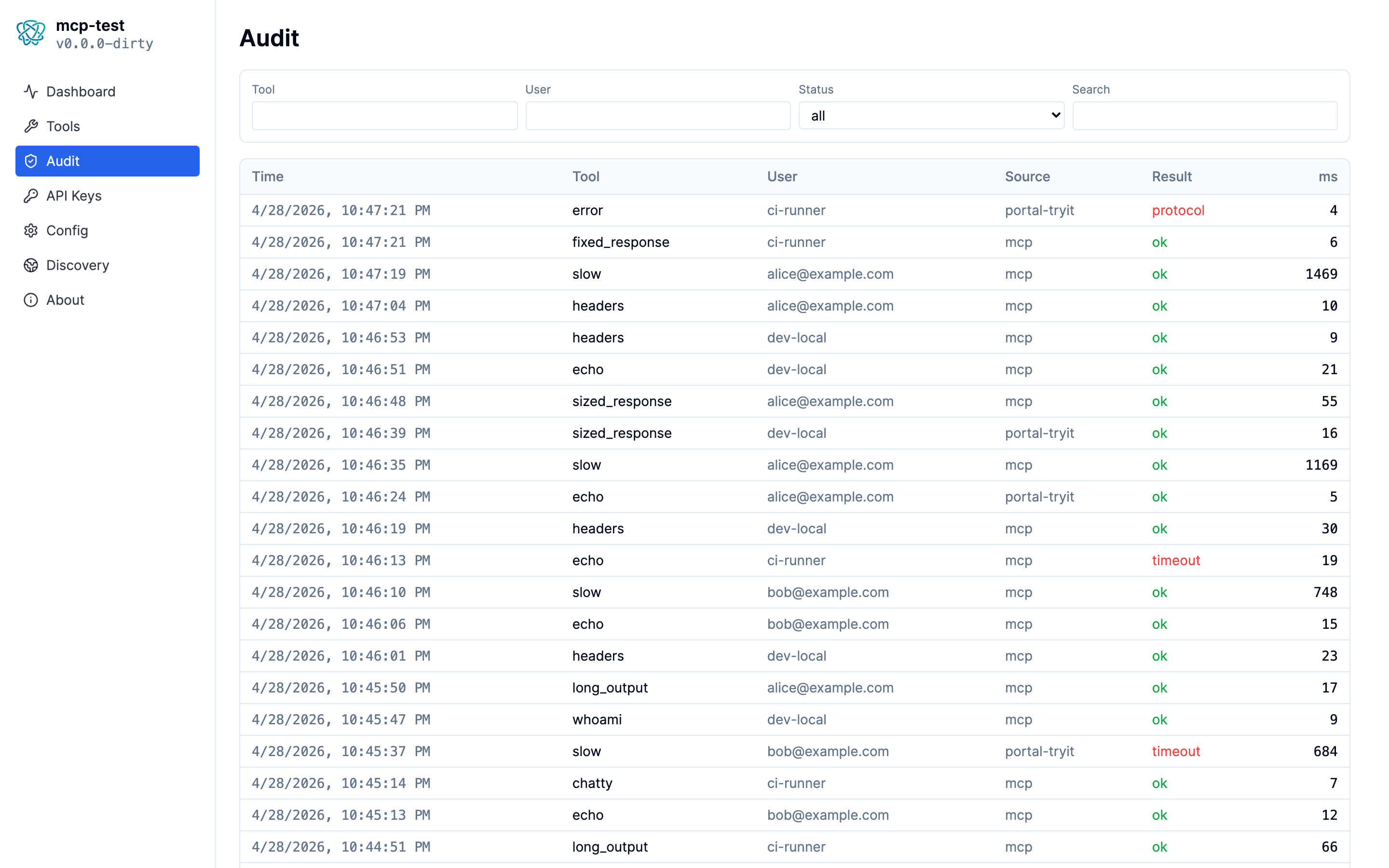
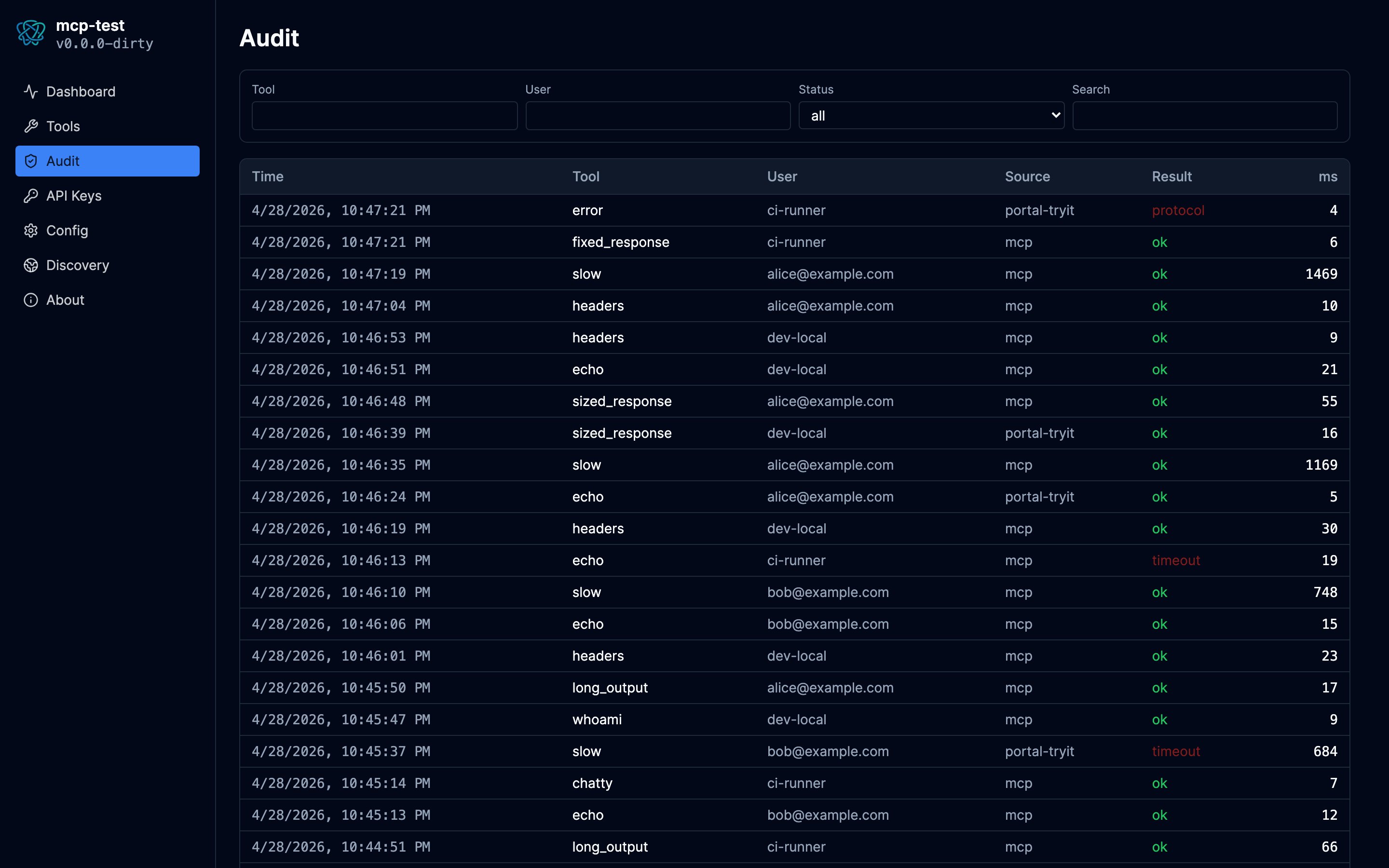
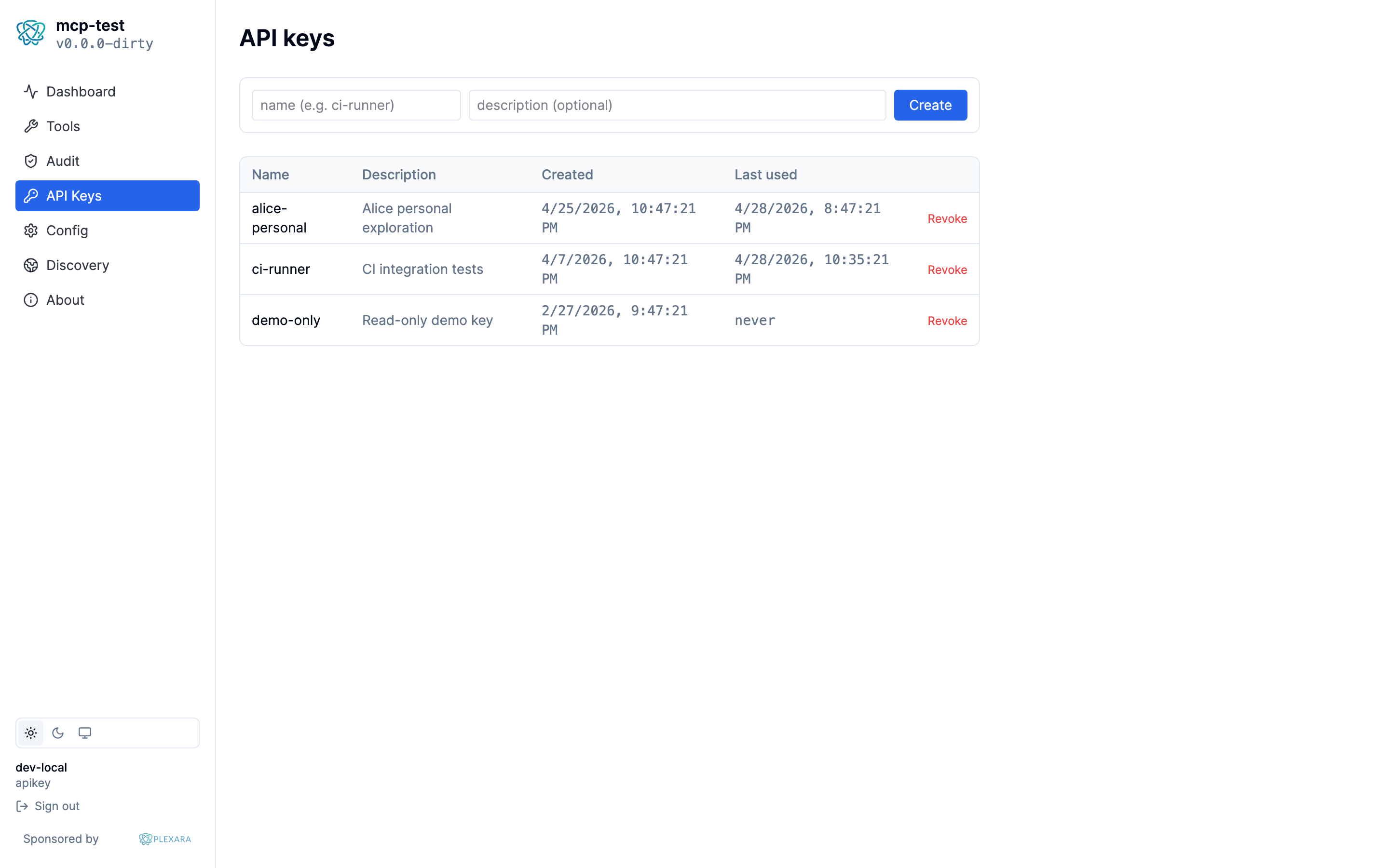
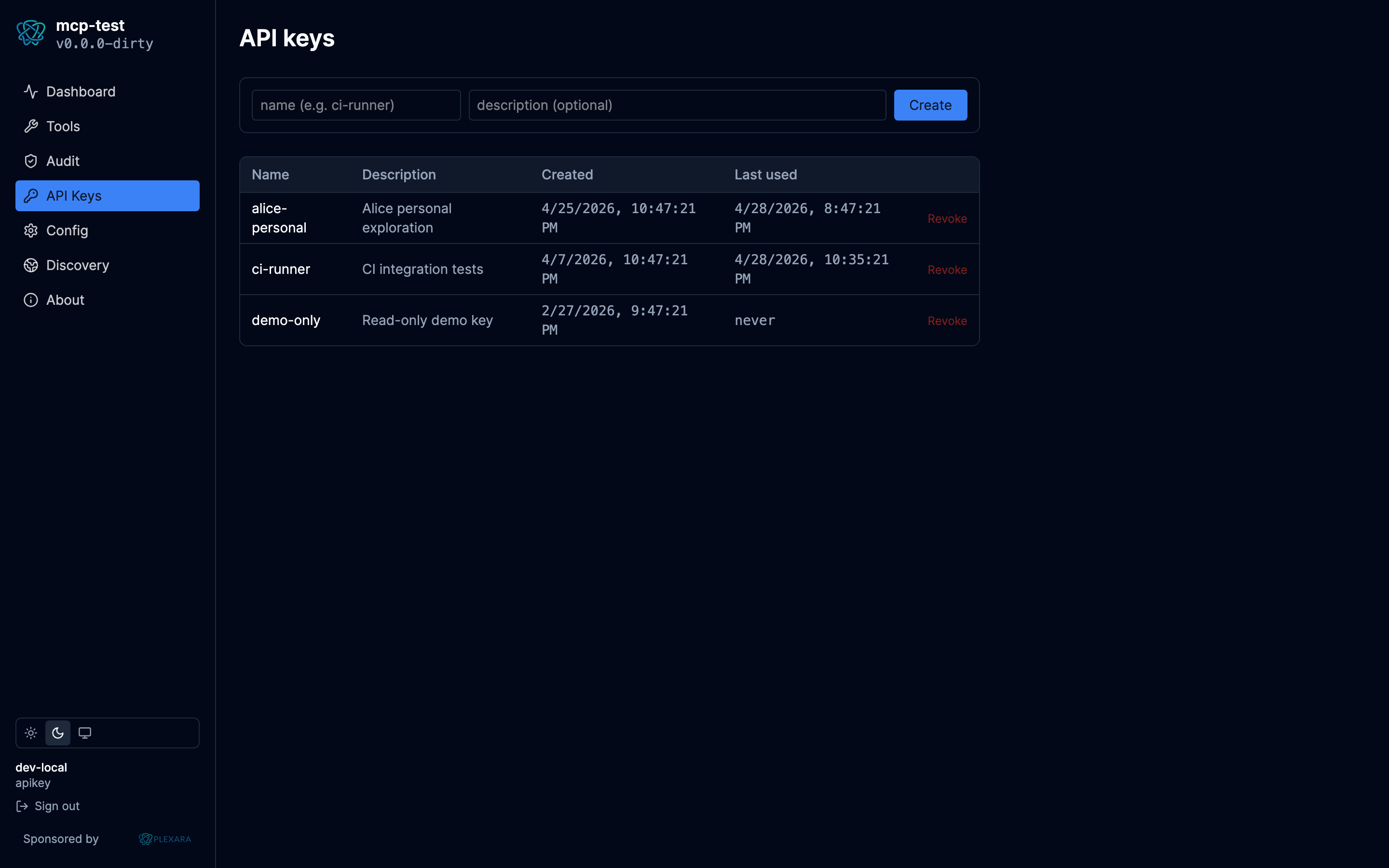
Audit log of every call
Postgres-backed timeline with sanitized parameters, identity, latency, response size, and source. Browse, filter, and chart it in the embedded React portal.
Streamable HTTP at the root
Mounted at /, with browsers redirected to
/portal/ and MCP clients passing through. No path
conventions to fight.
Built-in instructions
The MCP initialize response includes server-level
instructions that clients surface to the LLM as system context,
telling models these tools are test fixtures, not data sources.
By Plexara
Plexara is a commercial MCP server with configurable enrichment built in. mcp-test is what we use to verify Plexara's gateway behavior end-to-end; we ship it as OSS so anyone building MCP integrations can use the same fixture.
Why a separate test server
Pair mcp-test with the audit log and you can write end-to-end assertions about gateway behavior without running fragile real-data fixtures.
-
Tools that return the same output for the same input
(
fixed_response,loremwith a seed). -
Tools that fail on demand and on a schedule
(
slow,flakyseeded for reproducibility). -
Tools that emit progress notifications you can count
(
progress). -
Tools that echo identity and headers so you can confirm what's
being forwarded (
whoami,headers).